
6 Ways to Protect Sensitive Data in Logs
In May 2018, Twitter stated that they detected a vulnerability that unintentionally entered user credentials into their logging system. A year later, Facebook urged all

In May 2018, Twitter stated that they detected a vulnerability that unintentionally entered user credentials into their logging system. A year later, Facebook urged all
You may need to commit more effort and resources to ensure that your IT infrastructure is appropriately monitored and protected as it becomes more extensive,
Plain-text log maintenance is a thing of the past. While plain-text data is still helpful in certain situations, it pays to invest in reliable log
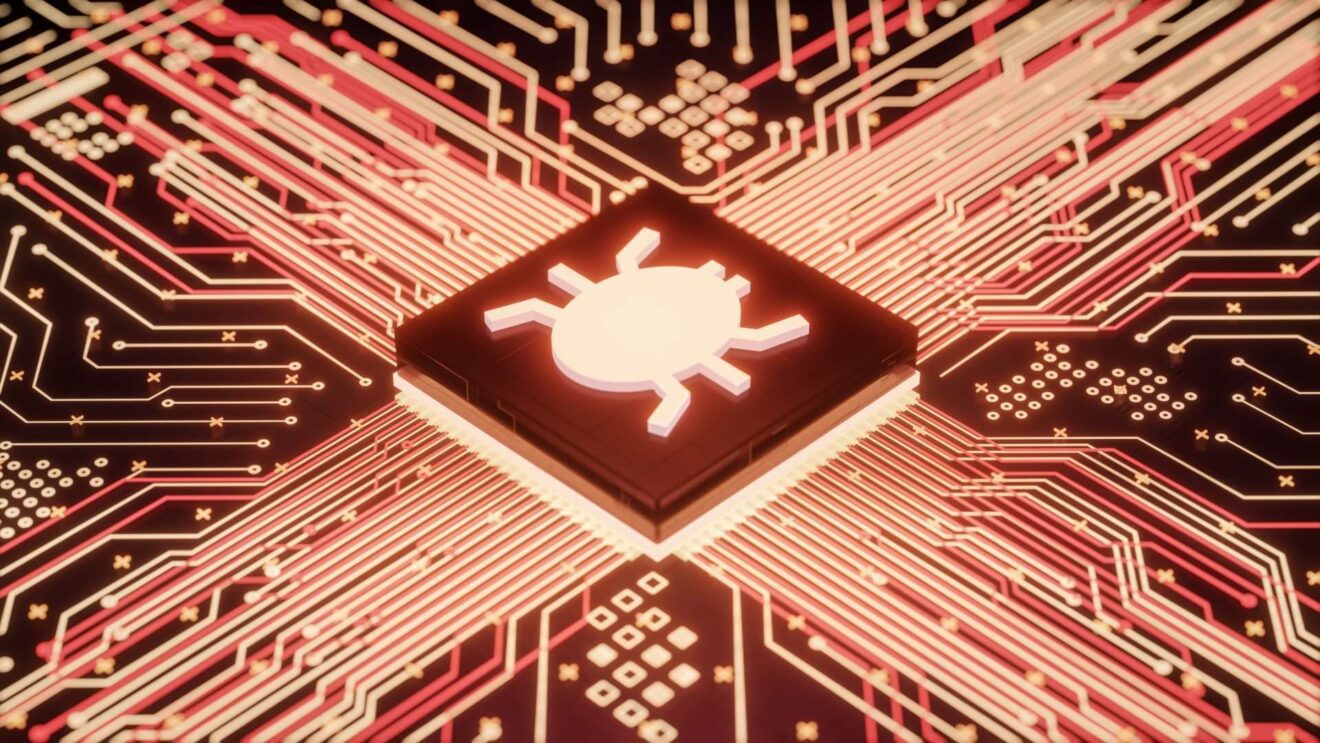
What’s Log4j? What is it used for? Log4j is a widely used Java logging library used in many Java enterprise applications. Because logging is so

What’s Log4j? What is it used for? Log4j is a popular Java logging library widely used in many Java enterprise applications. Because logging is so

As a business, you’re bound to have large numbers of interactions with customers, prospects, employees, consultants, partners, and third-party vendors. These interactions generate huge amounts
New secure platform delivers an ideal user experience and peace of mind for businesses. Apica Systems, the leader in service-level assurance, announced its unified platform
Spring Boot is a Spring module that combines embedded servers with the Spring Framework. It enables rapid application development on the Spring framework and provides
When large software and services are split down into micro applications or microservices, they become simpler to maintain. Microservice design has grown popular among developers